Is Your Web Application Safe From Web Attack ?
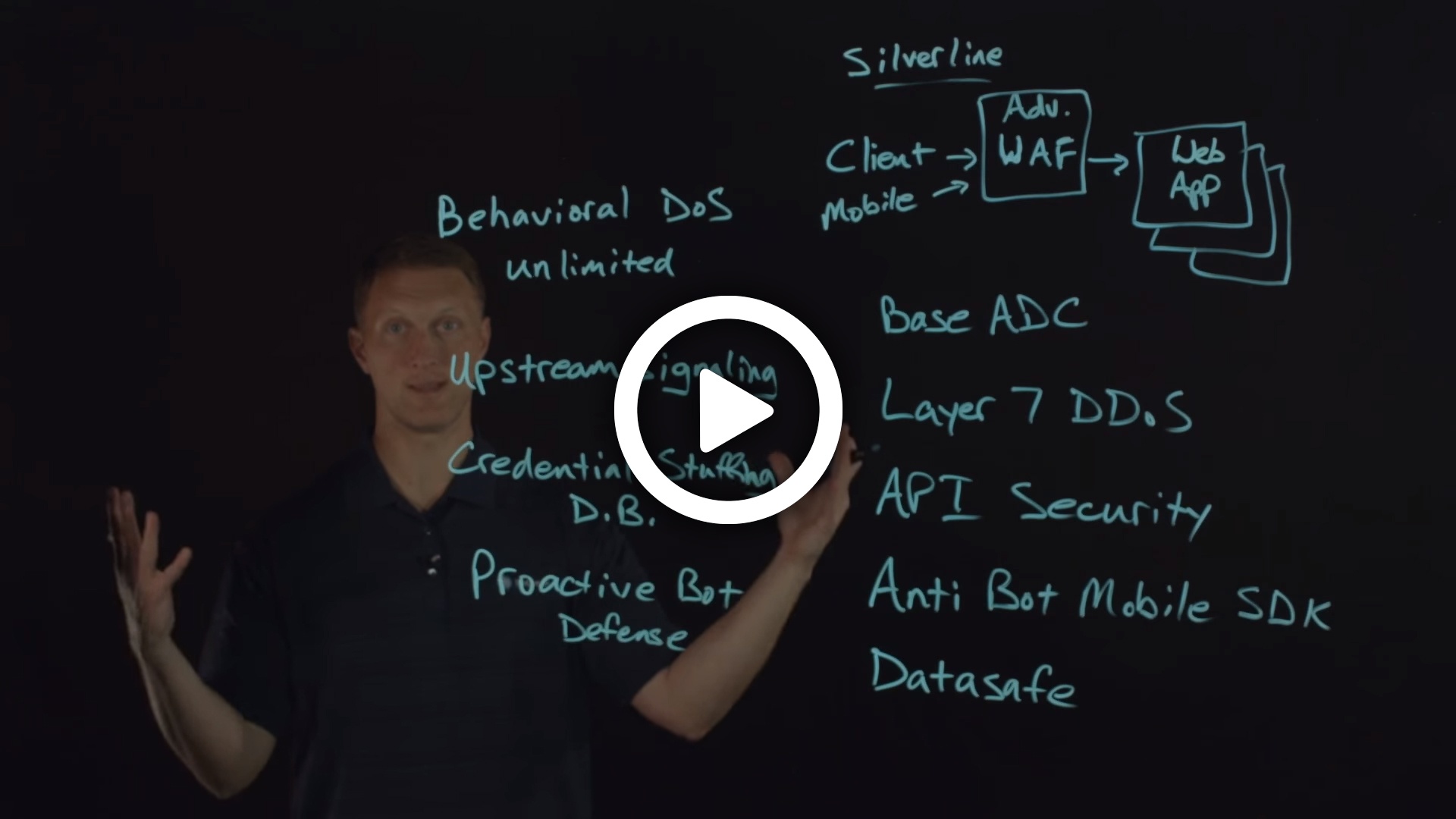
The F5 Advanced Web Application Firewall (WAF) provides a powerful set of security features that will keep your Web Applications safe from attack. Mny WAFs offer a basic level of protection from attack at the higher layers of the OSI stack, but the F5 Advanced WAF takes things even further and offers some serious security features like Anti Bot Mobile SDK, Credential Stuffing threat feeds, Proactive Bot Defense, and Datasafe to name a few. In this video, John outlines many of the exciting features offered in the F5 Advanced WAF.